Our lab, co-supervised with Naoyasu Ubayashi, had a welcoming BBQ party for new students, with distinguished collaborators and guests, including Nobukazu Yoshioka, Shinobu Saito, and Jialong Li. We really had a good time!
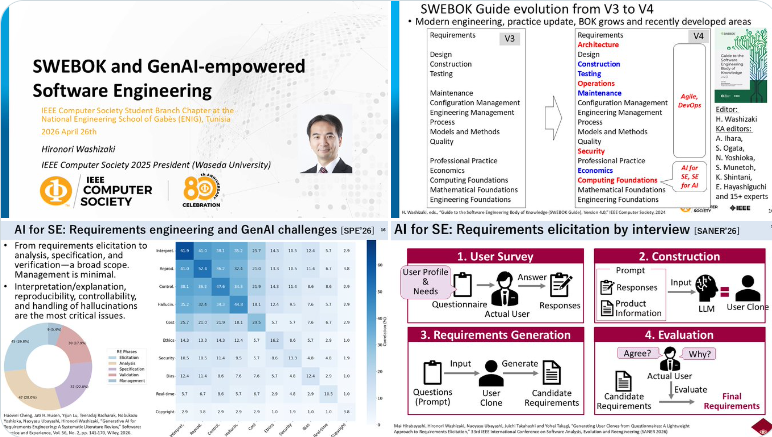
Prof. Washizaki provided his invited talk at the online workshop held by the IEEE Computer Society Student Branch Chapter at the National Engineering School of Gabès (ENIG)
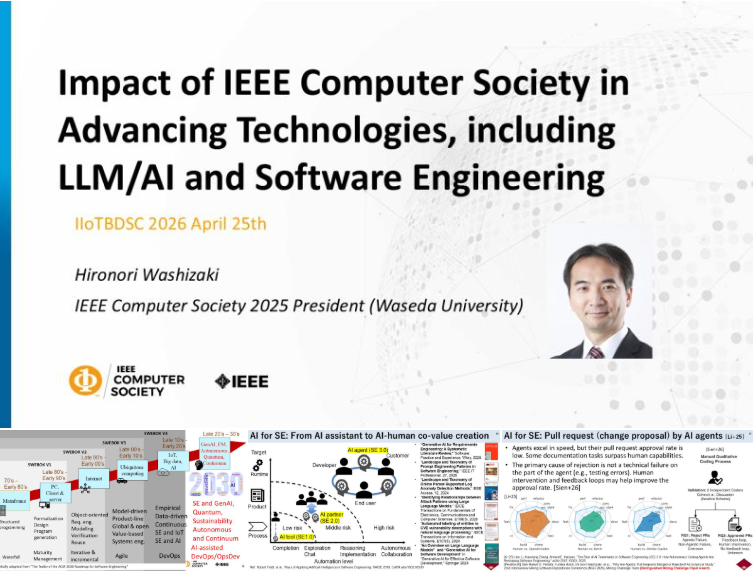
Prof. Washizaki provided his keynote at the International Conference on Industrial IoT, Big Data and Smart Cities (IIoTBDSC 2026)
Thanks to Prof Prof Victor Chang and organizers, Prof. Washizaki was delighted to be invited to provide his keynote, titled “Impact of IEEE Computer Society in Advancing Technologies, including LLM/AI and Software Engineering,” at the International Conference on Industrial IoT, Big Data and Smart Cities (IIoTBDSC 2026), Hong Kong, and online.
Prof. Amine Mhedhbi from Polytechnique Montreal visited our lab.
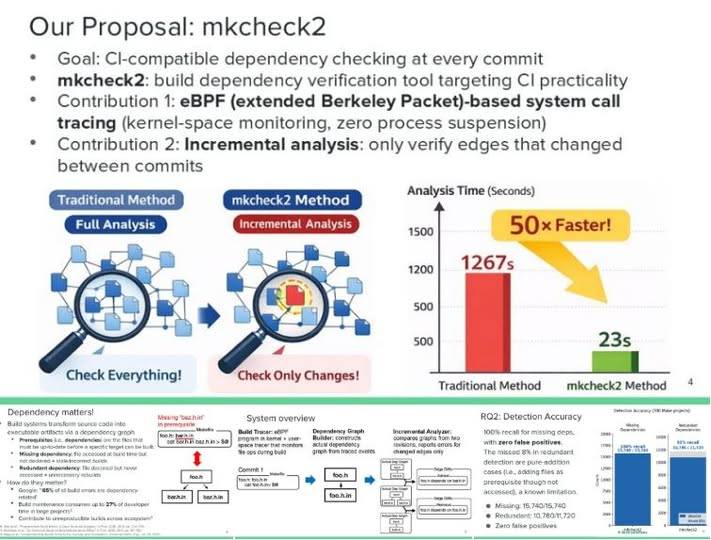
ICSE 2029 presentations
At the ICSE 2029 and its co-located events, Prof. Washizaki presented the followings.
- Research Track: Efficient Build Dependency Verification Using eBPF and Incremental Analysis
- Plenary: Introduction to ICSE 2029 in Japan
- SWEBOK Summit: Introduction of the Guide to the Software Engineering Body of Knowledge and Certification Program
- SERS: SWEBOK & Research Software
SWEBOK Summit 2026 was over!
Thanks to all organizers, committee members, authors, and participants, as well as the IEEE Computer Society’s support, the second edition of the SWEBOK Summit was successfully held at ICSE 2026, Rio. It is a great opportunity to bring together SWEBOK-related practices, case studies, education programs, potential future extension ideas, and grow our community.
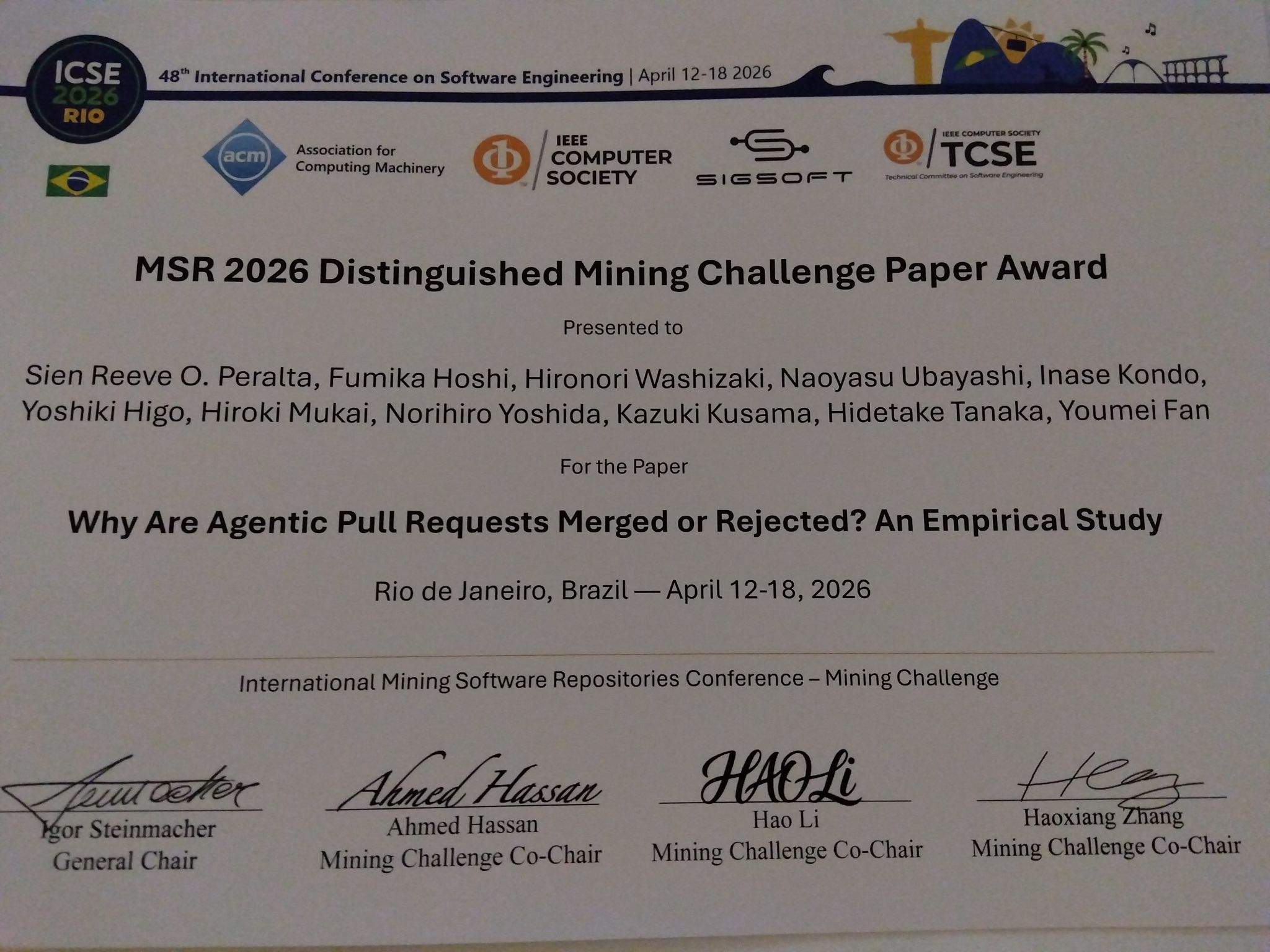
MSR 2026 Distinguished Mining Challenge Paper Award
MSR 2026 Distinguished Mining Challenge Paper Award was presented for the paper “Why Are Agentic Pull Requests Merged or Rejected? An Empirical Study.” Congrats, all! The poster was successfully presented by Youmei Fan. This is the result of joint work led by Sien Reeve Peralta and Fumika H. from our lab, with Osaka University, Ritsumeikan University, and NAIST, originating from the AI-Driven Software Engineering Summit sponsored by IPSJ-SIGSE.
- Sien Reeve Peralta, Fumika H., Hironori Washizaki, Naoyasu Ubayashi, Inase Kondo, Yoshiki Higo, Hiroki Mukai, Norihiro Yoshida, Kazuki Kusama, Hidetake Tanaka, Youmei Fan, “Why Are Agentic Pull Requests Merged or Rejected? An Empirical Study,” 23rd International Mining Software Repositories Conference (MSR 2026), Mining Challenge Track, Rio de Janeiro, Brazil, April 13-14, 2026.
IEEE COMPSAC 2027 Tokyo site visit
IEEE COMPSAC 2027 (IEEE Computer Society’s signature conference) will be hosted at IPUT, Shinjuku, Tokyo, Japan. Its organizing and local teams welcomed the site visit by the COMPSAC standing chair, Sheikh Iqbal Ahamed, PhD, to discuss the organization and venue. It must be one of the best ever COMSACs and an exiciting conference! Prof. Washizaki will serve as its honorary general co-chair.
As part of the IEEE Systems Council’s Interview Series, Washizaki was pleased to be interviewed by Stephen Ibaraki
As part of the IEEE Systems Council’s Interview Series, Washizaki was pleased to be interviewed by Stephen Ibaraki about his life, career, professional service and activities (particularly in IEEE CS), research interests, and future plans, with a particular focus on software engineering and AI.